
Most cyberattacks don’t look malicious anymore; rather, they’re as normal as they can be. An email arrives from a known vendor, the tone matches past conversations, the timing aligns with an active transaction... Nothing triggers suspicion until money moves or data leaks
This is the gap traditional security models struggle with, and is exactly where behavioral analytics in cybersecurity helps.
Behavioral analytics is an approach that focuses on patterns of activity over time, like how users communicate, how systems behave, and how data moves. Instead of scanning for known threats, it builds a baseline of what “normal” looks like and flags deviations.
In practice, this means continuously observing signals such as:
And much more… The key idea is simple - even the most convincing attack introduces subtle inconsistencies. Behavioral analytics is designed to catch those inconsistencies early.
This matters more now because attackers have changed tactics. Rather than sending obvious malware or spam, they often compromise real accounts, study communication threads, and insert themselves into ongoing conversations. This obviously poses detection challenges, as at that point, there is no “known bad signature” to match. The only thing that gives the attack away is behavior.
Signature-based detection is the traditional model used in many legacy security systems. It works by comparing files, messages, or activities against a database of known threat patterns, often called signatures. If a match is found, the threat is blocked or flagged. If not, the transaction or activity continues.
This model has been effective for years, especially against known malware families, previously identified phishing campaigns, and repeat attack patterns. But it has a fundamental limitation - it can only detect what has already been seen and documented. Anything new, slightly modified, or context-driven anomaly can bypass it.
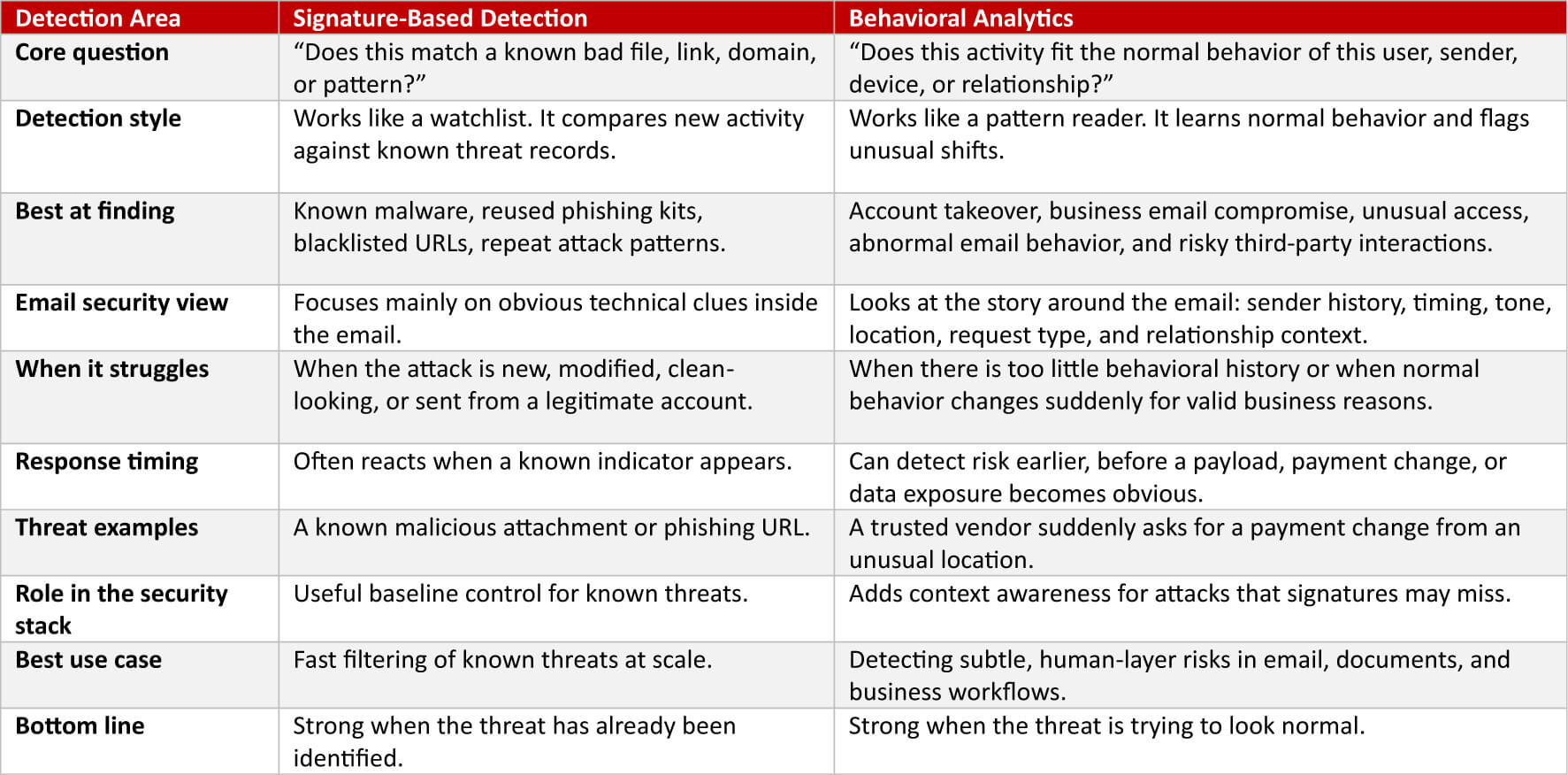
The real distinction between behavioral analytics and signature-based detection is not technical; it’s conceptual.
Signature-based systems answer, “Have we seen this before?” while behavioral analytics answers, “Does this make sense?” This shift becomes critical in modern environments where attacks are personalized, context-aware, and often executed through legitimate channels.
Email is now the primary entry point for most business-critical communication, including contracts, invoices, approvals, and sensitive documents. And it’s also where behavioral analytics becomes a key, as traditional defenses will only look for malicious attachments, suspicious links, or blacklisted domains.
But many high-impact attacks avoid all these; instead, attackers rely on compromised internal or partner accounts, familiarity with business workflows, and precise timing aligned with real transactions. From a system’s perspective, nothing looks “malicious,” but from a behavioral perspective, everything feels slightly off.
This is why behavioral analytics is increasingly applied directly to email interactions, not just networks or endpoints.
Tools like endpoint detection and response (EDR) play an important role in modern security. They monitor activity on devices like tracking processes, memory behavior, and system-level anomalies. They are effective when malware executes on a device, unauthorized processes run, or any suspicious system activity occurs.
But there’s a growing blind spot. Many modern attacks succeed without triggering endpoint activity at all. If an employee receives a convincing email and voluntarily shares data or approves a transaction, nothing malicious runs on the endpoint. From an EDR perspective, the system remains clean.
Behavioral analytics fills that gap by analyzing the human layer of security - the interactions that happen before any technical compromise. Consider a simple scenario:
Individually, these signals may seem minor, but together, they indicate risk. And that’s precisely the difference between pattern recognition and context awareness. Legacy tools tend to react AFTER something breaks; behavioral analytics aims to detect risk during the setup phase.
This aligns with the idea that attacks don’t start with execution; they start with observation and preparation. By the time malware is delivered or a transaction is manipulated, the attacker has already spent time understanding the environment. Behavioral analytics tries to intercept that process earlier, when the signals are subtle but still detectable.
Modern security is moving toward systems that:
Because the reality is your biggest risk often sits outside your network - inside conversations, shared files, and third-party interactions.
Behavioral analytics then becomes significantly more powerful when applied directly to email and content flows. Solutions like RMail by RPost focus on securing the email layer itself, adding visibility into delivery, interactions, and message handling.
Building on that, another solution, RAPTOR™ AI, applies behavioral intelligence across communications, analyzing patterns of interaction, third-party exposure risks, and early reconnaissance signals.
This shifts security from reacting to threats to pre-empting them. And in a world where attacks are designed to blend in, that distinction matters more than ever. Because the most dangerous threats aren’t the ones that look malicious; they’re the ones that look completely normal - until they aren’t.

May 05, 2026

April 22, 2026

April 17, 2026

April 03, 2026

March 27, 2026