It’s finally Blaber Fronday! We’re offering a money saving deal for e-sign, e-security and file sharing that happens only once a year. These days, if you want a memorable catchphrase, you opt for the portmanteau—where two words or names become one (e.g. “brunch”, “chillax”, “Brangelina”). Everybody’s doing it—even health policy wonks (“twindemic”, “tripledemic”) and economists […]
Inflation Makes the “Tesla of E-Sign” Even More Appealing…Think, Almost No Operating Cost, All Electric In the world of car branding (and marketing in general), there’s the “good, better, best” concept, which was pioneered by General Motors in the 20th century. Think back to a time where men wore hats, were the sole breadwinner in […]
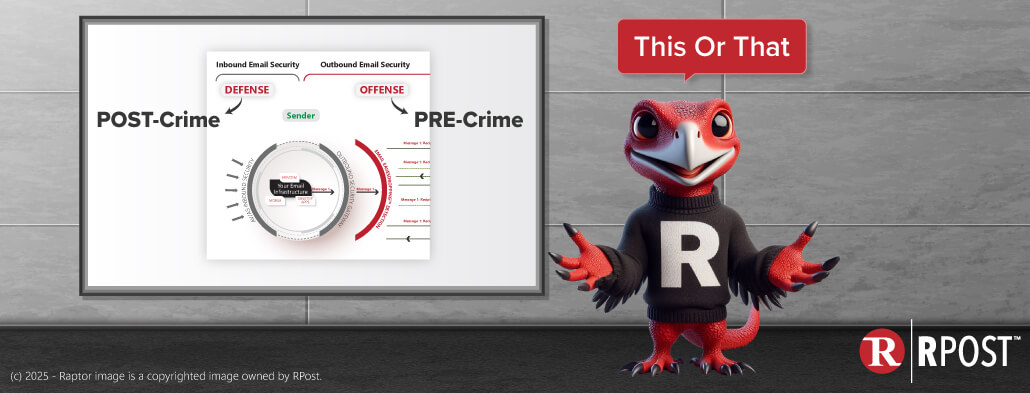
Working from Home Continues to Test Patience of IT Administrators Has this happened to you recently: You get an email from yourself asking you to click a link to see an agenda you didn’t write or for an invoice you never sent? The newest are people sending you pictures of checks that they supposedly put in the […]
July 18, 2025

July 11, 2025

July 04, 2025

June 27, 2025

June 18, 2025